- Security >
- Firewall Configuration
Firewall Configuration¶
On this page
Overview¶
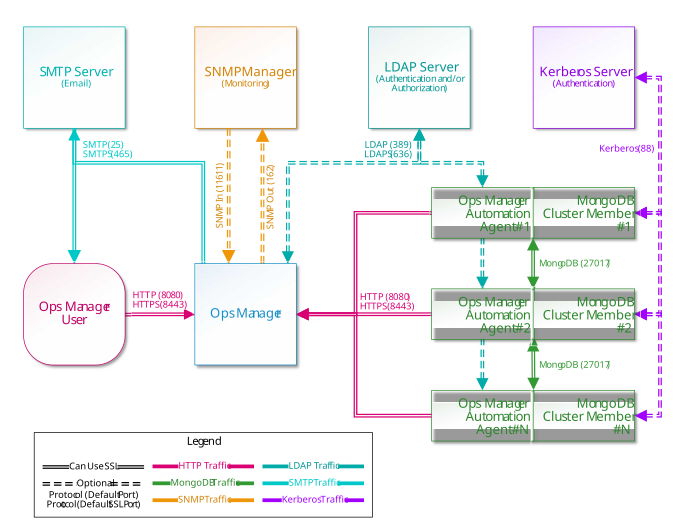
Ops Manager connects with a number of services which may also use SSL. This page explains the necessary ports to deploy the various components used with an Ops Manager deployment.
Accessible Ports¶
The Ops Manager application must be able to connect to users and Ops Manager agents over or Secure HTTP (HTTPS). Ops Manager agents must be able to connect to MongoDB client MongoDB databases.
Though Ops Manager only requires open HTTP(S) and MongoDB network ports to connect with users and to databases, what ports are opened on a firewall depend upon what capabilities are enabled: encryption, authentication and monitoring.
This page defines which systems need to connect to which ports on other systems.
Important
To run Ops Manager without an Internet connection, see Configure Local Mode for Ops Manager Servers without Internet Access to ensure you have all of the necessary binaries to run Ops Manager without an Internet connection.
Ports Required to Use Ops Manager¶
- Both Ops Manager users and Ops Manager agents must be able to connect to Ops Manager application over HTTP(S). See Manage Ops Manager Ports to set a non-default port for Ops Manager.
- Ops Manager must be able to connect to the backing MongoDB databases
running
mongod. - For each Ops Manager group, Ops Manager agents must be able to connect to all
client MongoDB processes (
mongodormongos). - The Ops Manager application must also be able to send email to Ops Manager users.
To use Ops Manager, open the following ports to the specified servers.
| Service | Default Port | Transport | Direction | Purpose | Uses SSL? |
|---|---|---|---|---|---|
| HTTP | 8080 | TCP | Inbound | Web connection to Ops Manager from users and Ops Manager agents. | No |
| HTTPS | 8443 | TCP | Inbound | Web connection to Ops Manager from users and Ops Manager agents. | Yes |
| HTTP(S) | 8090 | TCP | Inbound | Provides a health-check endpoint for monitoring Ops Manager through a monitoring service like Zabbix or Nagios. This is disabled by default. To enable it, see Enable the Health Check Endpoint. When enabled, you can access the endpoint at: The API endpoint provides the ability to check connections from the HTTP Service to the Ops Manager Application Database and the Backup Snapshot Storage. A successful response returns the following: |
Optional |
| MongoDB | 27000 - 28000 | TCP | Both | Connect to MongoDB application, backup and client databases. | Optional |
| SMTP | 25 | TCP | Outbound | Send emails from Ops Manager. | No |
| SMTPS | 465 | TCP | Outbound | Send emails from Ops Manager. | Yes |
Ports Needed to Administer Ops Manager¶
Most Ops Manager administration can be performed through the user interface. Some procedures require access to the operating system. To permit your administrators to access your Ops Manager and MongoDB servers, open the following ports to those servers.
| Service | Default Port | Transport | Direction | Purpose | Uses SSL? |
|---|---|---|---|---|---|
Secure Shell (ssh) |
22 | TCP | Inbound | Linux System administration. | Yes |
| Remote Desktop Connection (RDP) | 3389 | TCP | Inbound | Windows System administration. | No |
Ports Needed to Integrate Ops Manager with SNMP¶
To send and receive SNMP messages to and from your MongoDB deployments must open the following ports between Ops Manager and your SNMP Manager.
| Service | Default Port | Transport | Direction | Purpose | Uses SSL? |
|---|---|---|---|---|---|
| SNMP | 162 | UDP | Outbound | Send Traps to SNMP Manager. | No |
| SNMP | 11611 | UDP | Inbound | Receive requests from SNMP Manager. | No |
See SNMP Heartbeat Settings to set SNMP to use non-standard ports.
Ports Needed to Authenticate with Ops Manager¶
MongoDB Enterprise users can use LDAP to authenticate Ops Manager users. To authenticate using LDAP, open the following ports on Ops Manager and your LDAP server.
| Service | Default Port | Transport | Direction | Purpose | Uses SSL? |
|---|---|---|---|---|---|
| LDAP | 389 | UDP | Both | Authenticate and/or authorize Ops Manager users against LDAP server. | No |
| LDAPS | 636 | UDP | Both | Authenticate and/or authorize Ops Manager users against LDAP server. | Yes |
See Authentication through LDAP to configure LDAP URI strings including ports.
Ports Needed to Authenticate with MongoDB¶
MongoDB Enterprise users can use Kerberos or LDAP to authenticate MongoDB users. To authenticate using LDAP or Kerberos, open the following ports between the MongoDB client databases, Ops Manager and the Kerberos or LDAP server(s).
| Service | Default Port | Transport | Direction | Purpose | Uses SSL? |
|---|---|---|---|---|---|
| Kerberos | 88 | TCP / UDP | Outbound | Request authentication for MongoDB users against Kerberos server. | No |
| Kerberos | 88 | UDP | Inbound | Receive authentication for MongoDB users against Kerberos server. | No |
| LDAP | 389 | UDP | Both | Authenticate and/or authorize MongoDB users against LDAP server. | No |
| LDAPS | 636 | UDP | Both | Authenticate and/or authorize MongoDB users against LDAP server. | Yes |
See Kerberos Authentication to the Application Database to configure Kerberos for authentication to the Ops Manager application database.